Mission-Ready MVP: Web Interface for U.S. Defense-Grade Security Tool
Fast-Track Security Scanner interface in 30 Days. U.S. Air Force
- Delivering a functioning MVP of a unique software scanning solution within a 1-month timeframe
- The solution is used by the US government structures like AirForce and SpaceForce
- Performing frontend development services to create a Web Client for the initial scanning tool
- Industry:
- Cybersecurity
- Location:
- USA
- Duration:
- 4 months
- React
- Node.js
- MVP Development
- Design Development
- Frontend Development
- Architecture Consulting
- Project Management
- Web
Client overview
The Project
Our client represents a group of first-class engineers who work on a set of software products. Their main focus is to provide IT infrastructure for software applications and networks under the highest standards of security.
The Challenge
The client came to us with an initial request to create an MVP within a very limited timeframe. We were meant to finish the MVP development before the planned product demonstration date. We also had to take into account that the app is meant to be used by the US government structures like AirForce or SpaceForce where security is of paramount importance.

So after gathering the project requirements, it was obvious that the project consisted of two parts, and our responsibility lay in the web app development.
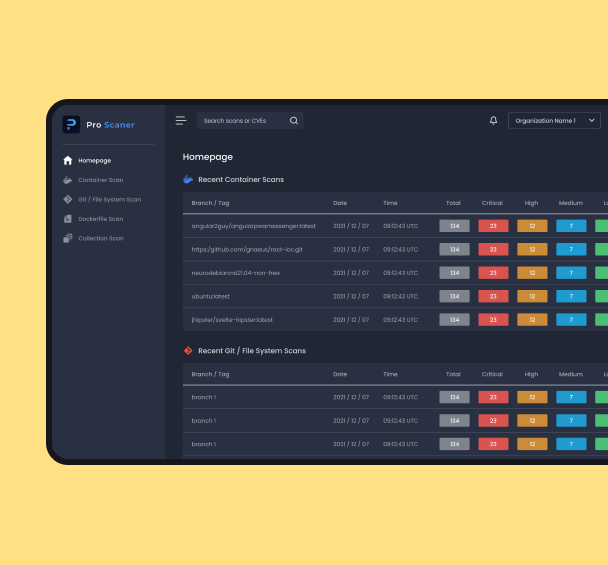
The scanning part was created by the client. Our task was to create a web application where an end-user can start the code scanning and see the results through a user-friendly web interface. To make it possible we needed to develop a Web Client for the initial scanning tool. We've thought through the required web architecture to reach the purpose.
Besides that, the client has previously worked with another agency that has delivered the app design. However, the result was unsatisfactory, so we have offered a new design that was well appreciated in the end.
Provided by Uinno
Core solutions
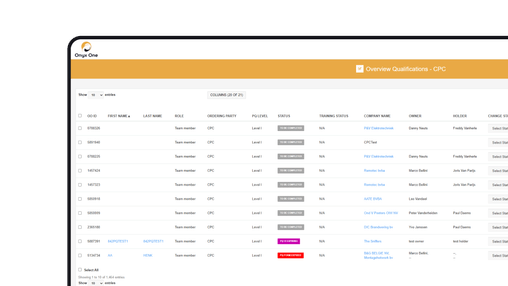
The project was tightly limited by the strict deadline so our app development team started right away. Our experts asked all the necessary questions and described the way we see the whole project, roughly estimated the project development, and defined how we can fit into the deadlines. The client liked our proposals a lot so we've moved on with the MVP development stage pretty fast.
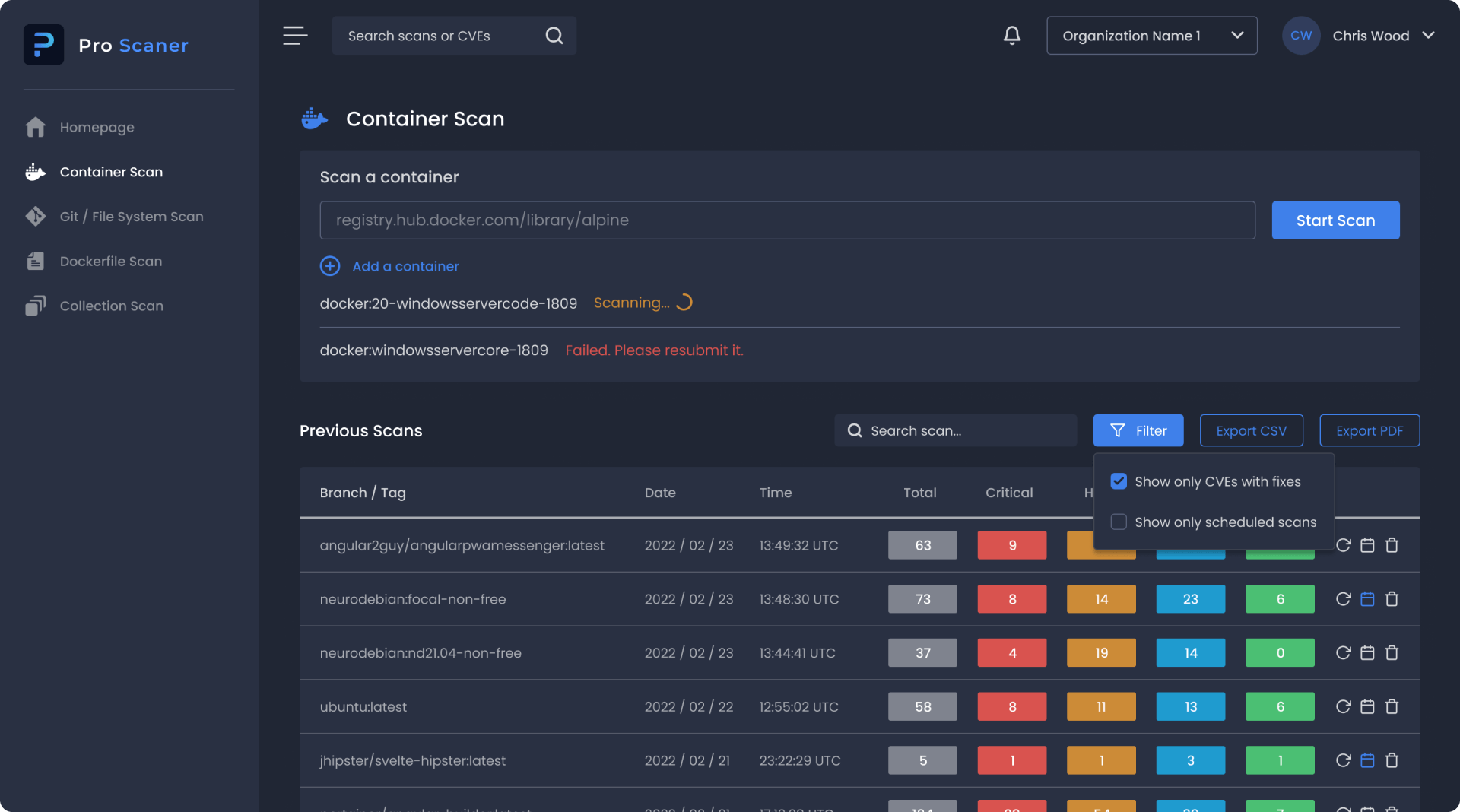
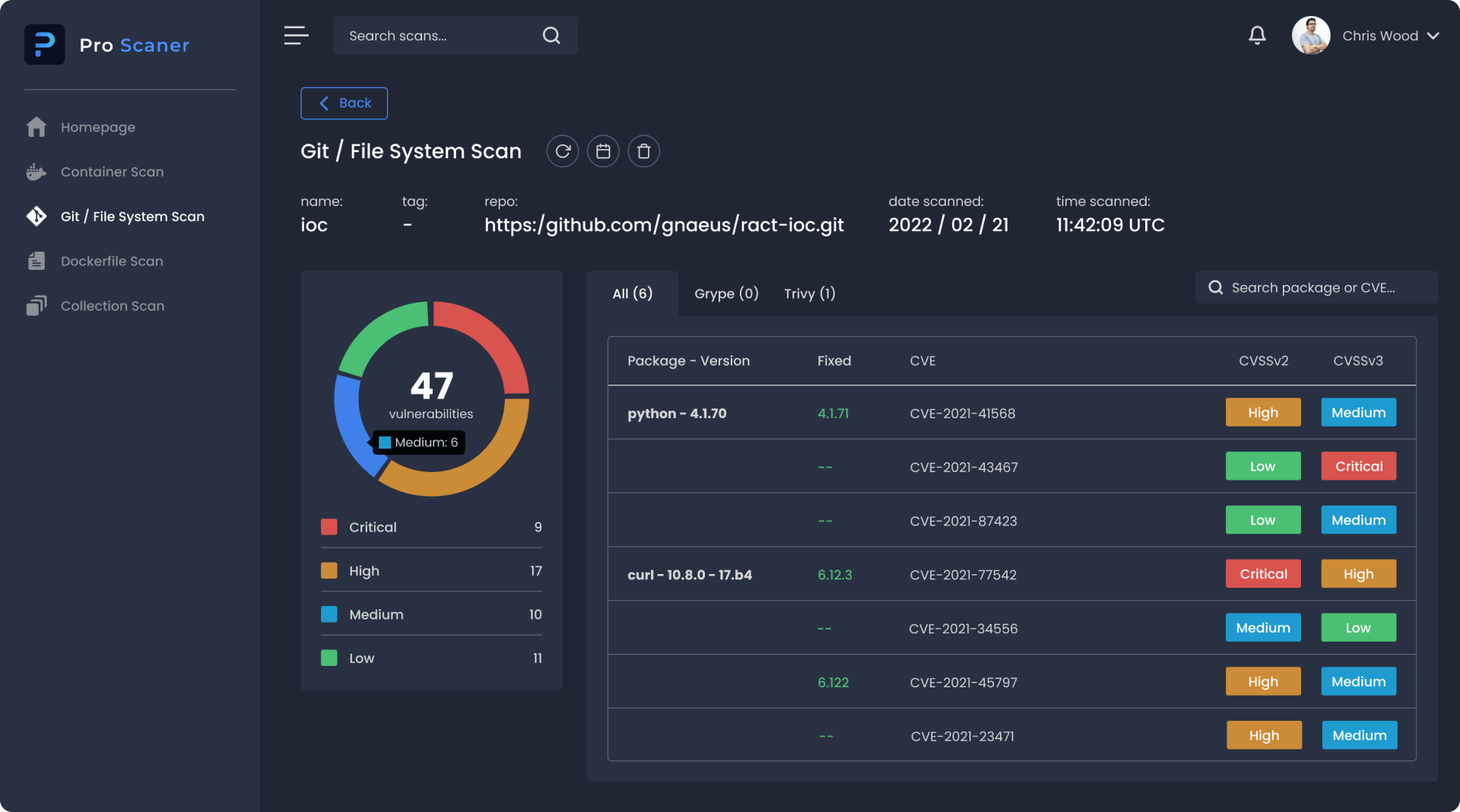
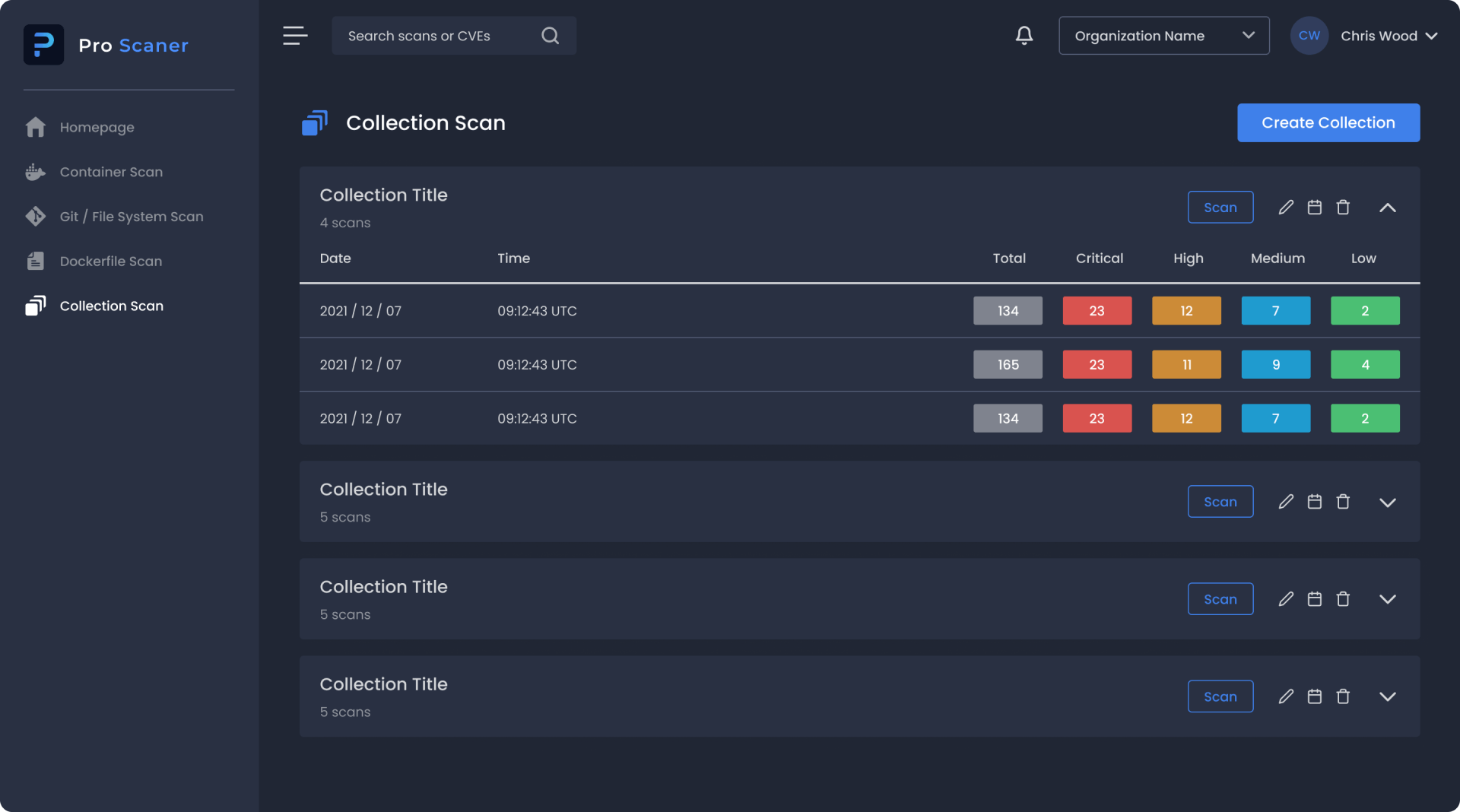
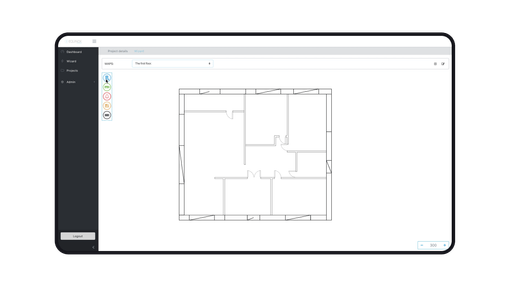
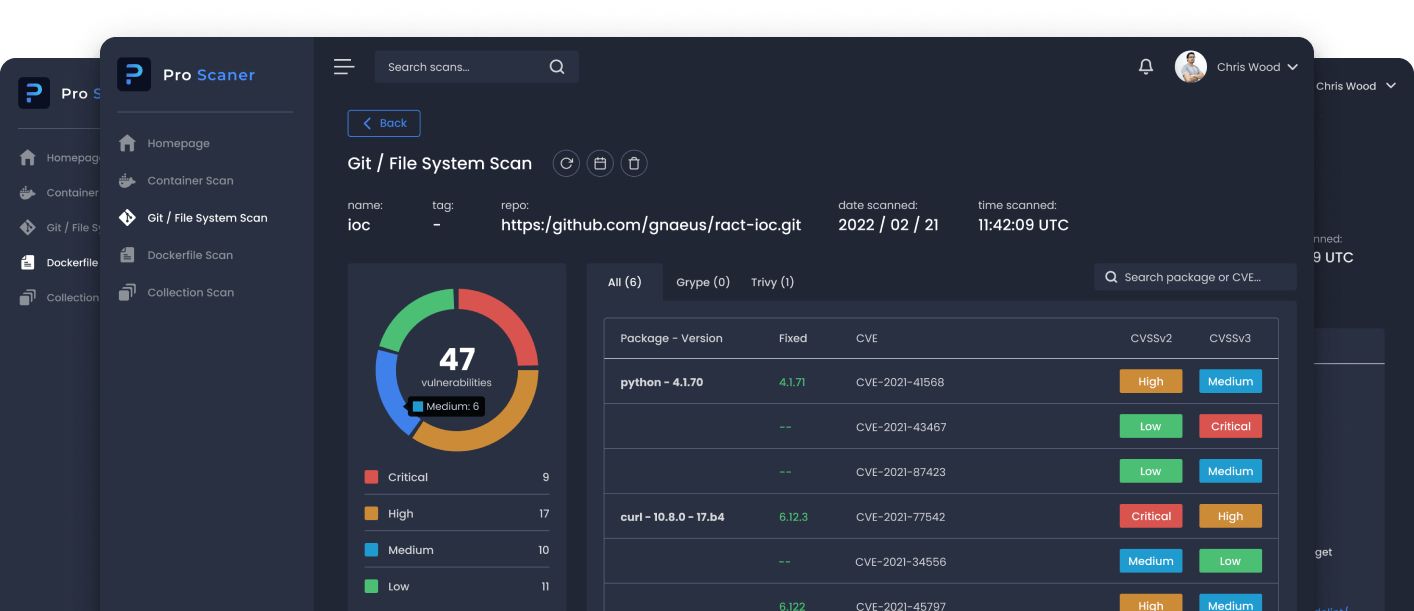
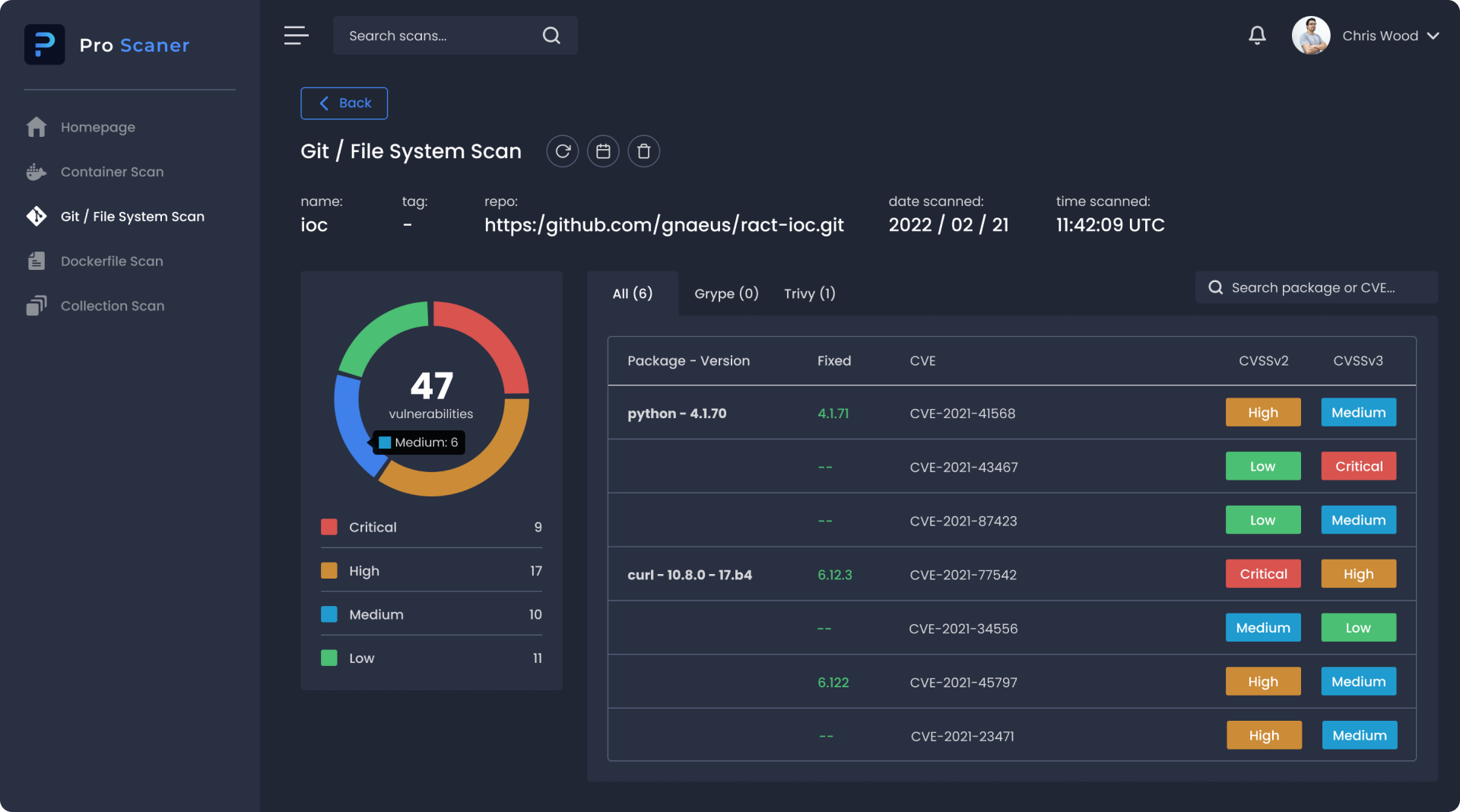
It is a web application specifically designed for engineers that scans three things:
- Docker containers;
- Docker images;
- Git Repositories.
First, the public ones and, after a while, it is meant to scan the private ones as well. How does it work?
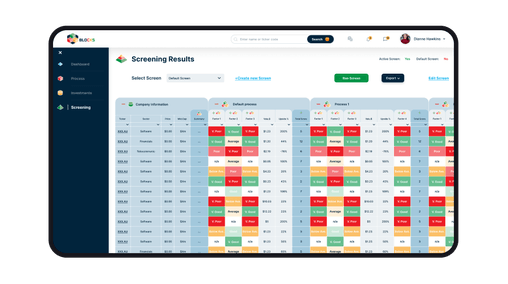
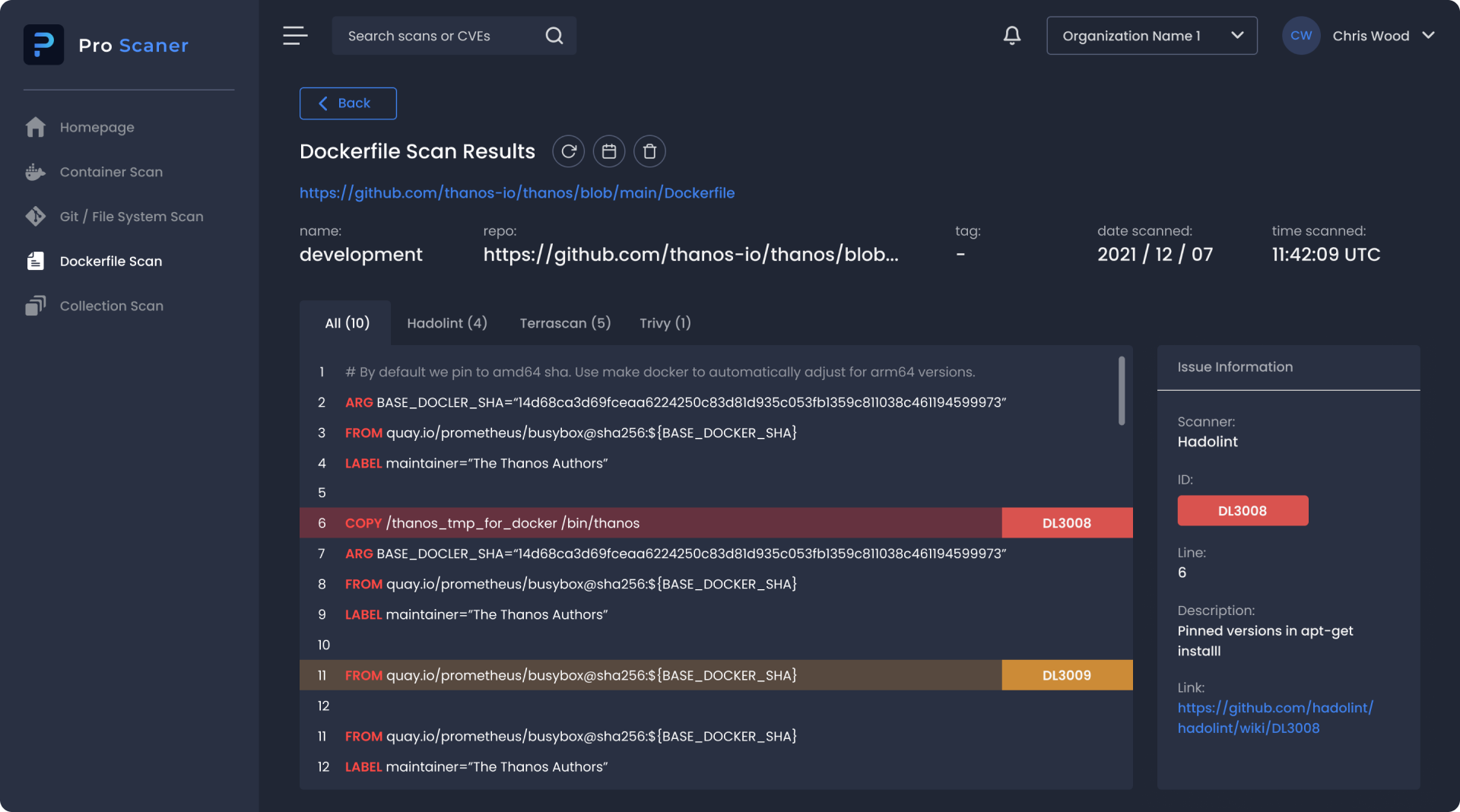
To scan a certain product for potential vulnerabilities, a user can provide a link to Git Repository, Dockerfile, or the name of the Docker Container from the DockerHub via a web interface. The scanning tool matches the product code with the database of the most common vulnerabilities. Once done, a user can see the detailed results on the web interface that shows the emphasized code lines and explicit explanations of the detected flaws.
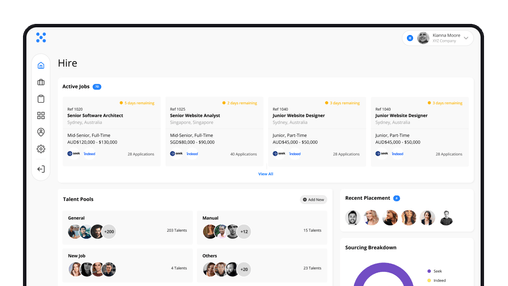
Besides the core functionality, we have implemented the following features:
The app demonstrates the scanning process of Docker containers, images, and Git repositories in a convenient graphic format.
The more thought-out the product becomes, the bigger amount of potential flaws it can detect.
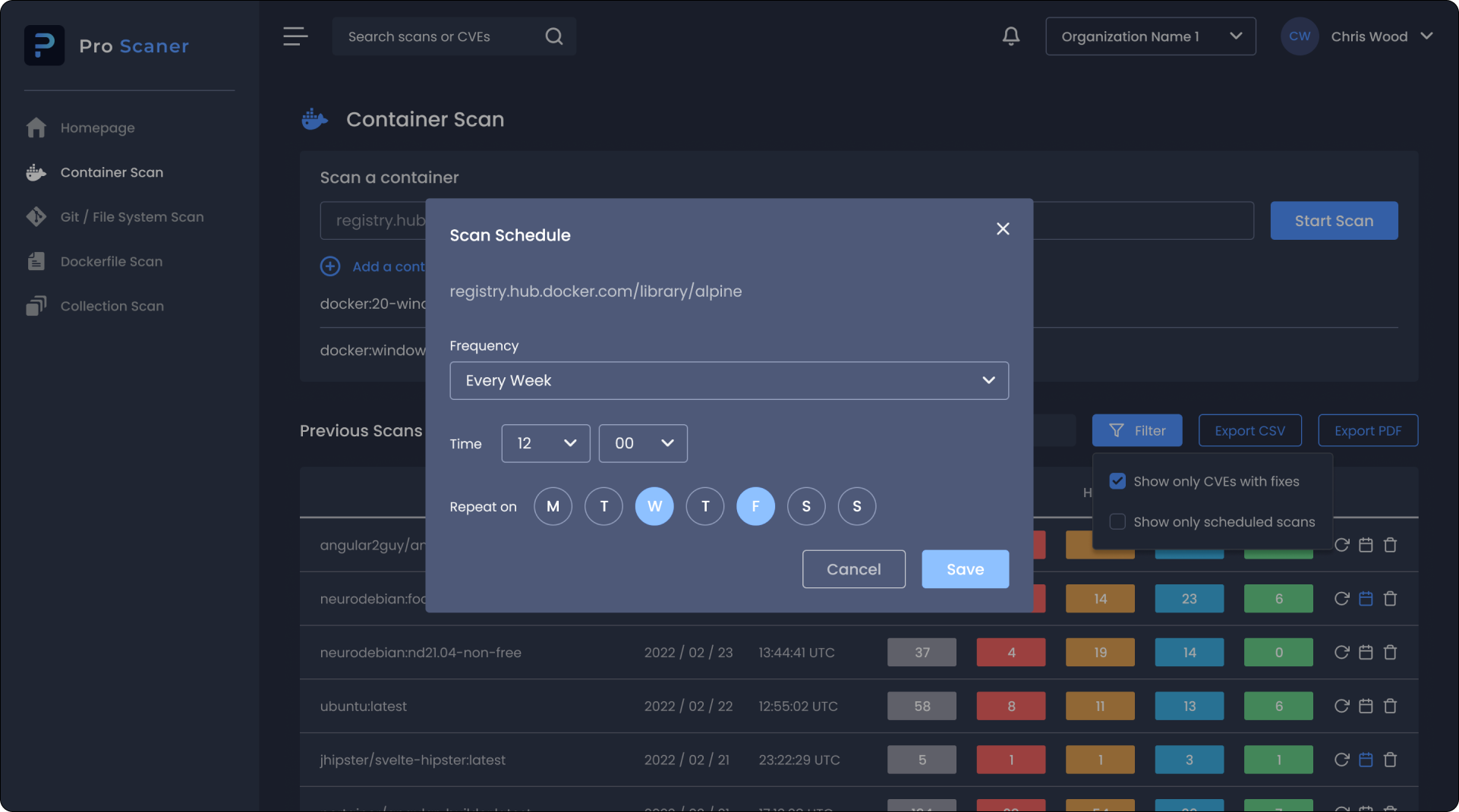
The predefined scanning schedule allows checking products for vulnerabilities that may not be even launched.
From starters, our experts have offered the technology stack by themselves based on the discussed business objectives. Node.js was the most suitable backend technology as real-time events were planned to be conducted there.
Likewise, to reduce the development time and meet the deadlines we've decided to buy the dashboard template that our clients liked very much. It turned out to have the React implementation. That is how React became our primary frontend development technology.
Ultimately, our development team consulted the client about the perfect architecture that was meant to connect frontend and backend into a well-functioning solution.
What's in the outcome?
The Uinno development team has managed to develop a unique software scanning solution within a 1-month timeframe.
It is a software security tool that scans any engineering system for vulnerabilities. If the development code contains a flaw, it shows the exact line of code with it. If the issue is with a certain integrated framework, the tool emphasizes and explains it.
Ultimately, the client who has wide experience in outsourcing IT projects is very satisfied with our communication, the speed of the problem resolution, and the quality of our work.
The product development continues and future releases have great chances to witness such functionality as billing processing and an even wider range of detected software vulnerabilities.
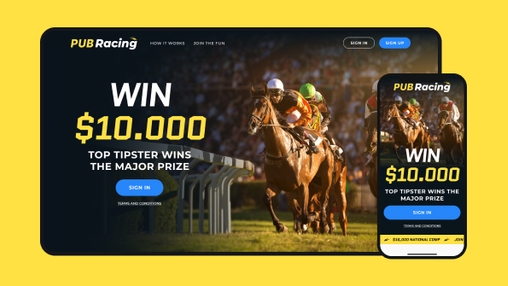
explore more projects
Uinno is a product development agency compiled of engineers and technology experts with an ownership mindset who are solely focused on solving business challenges via creating future-ready apps, websites, and digital solutions.
United Kingdom
Kingston upon Thames, 145 London Road
Estonia
Tallinn, Tornimae 5
Ukraine
Lviv, Hazova St. 7, Seven-G
Ukraine
Zaporizhzhia, Sobornyi 160
USA
447 Broadway 2nd floor
New York, NY 10013
USA
78 SW 7th St,
Miami, FL 33130
+380 (99) 455 99 91
contact@uinno.io
hr@uinno.io